What would you expect power plants, production facilities and transportation companies to have in common? They all use Operational Technology (OT) in sometimes highly critical infrastructures to control industrial systems. Examples include production lines, robot systems and machines, to name just a few.
Behind these are technologies such as Industrial Control Systems (ICS) or Supervisory Control and Data Acquisition (SCADA) systems. At the same time, most companies today also use the well-known Information Technologies (IT), which include data management, software and networks. Understanding the finer points of these areas is crucial to harnessing their potential, especially in terms of security aspects that protect our digital future.
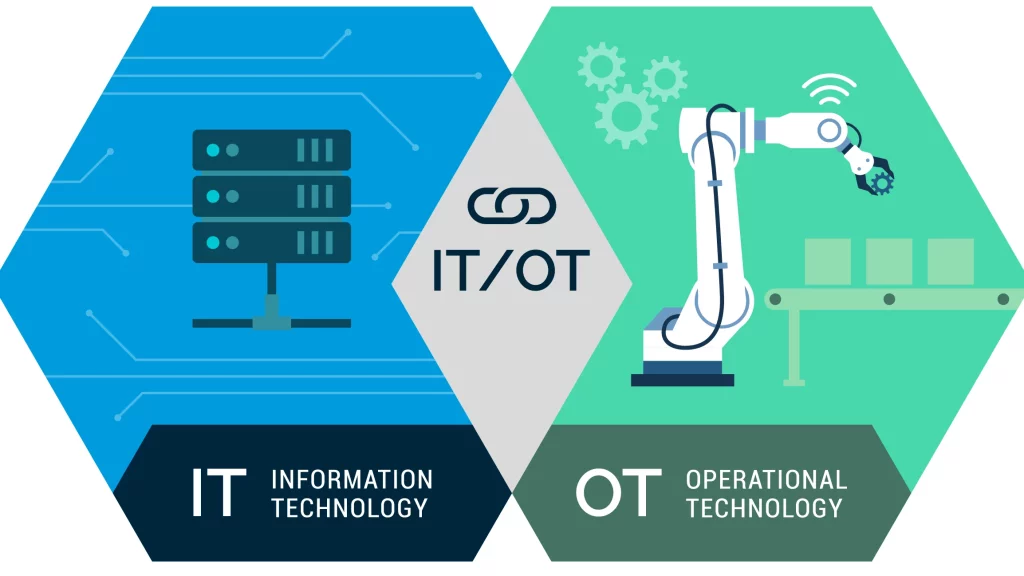
Table of contents
Operational Technology (OT): Digital Technology Meets Physical Reality
Operational Technology (OT) operates at the intersection between the physical and the digital, managing industrial processes and machinery. Technologies such as Industrial Control Systems (ICS), Supervisory Control and Data Acquisition (SCADA) systems and Programmable Logic Controllers (PCLs) collect data from sensors and control automated workflows in order to optimize the processes of manufacturing, energy generation, transport systems and much more in real time. They ensure the efficiency and safety of these processes and embody the synergy between technology and industry.
Information Technology (IT): Maintaining the Digital Ecosystem
Information Technology (IT) operates in the digital world and manages data, software, and networks. IT professionals develop applications, maintain databases, and ensure digital security. IT is the backbone of our digital existence and enables communication, data analysis, and the seamless functioning of various applications and systems.
Security Aspects: Safeguarding the Digital Landscape
Within the domains of OT and IT, security is paramount and comes as a top priority. Cyber threats loom large, necessitating robust security measures. In OT, security ensures the uninterrupted functioning of critical infrastructure while protecting against physical and cyber threats. In IT, the focus is on data security, network protection and user privacy to prevent cyberattacks, data breaches, and unauthorized access. Connecting OT and IT helps to improve and oversee operations as well as make better decisions, but it also makes it more difficult to manage and secure the systems. The use of special communication rules in OT systems makes the connection with standard IT systems more complex and increases possible risks.
Two protocols are presented as examples: International Electrotechnical Commission (IEC) 60870-5-104 (also known as IEC 104) and Telecontrol Application Service Element 2.0 (TASE.2), also known as Inter Control Center Protocol (ICCP). Both are crucial communication tools used in the electric power industry. They help to ensure that important information is shared quickly and reliably between control centers, substations, and other electricity supply companies, ensuring that electricity distribution runs smoothly. IEC 104 is mainly used for communication between control centers and substations. It shares measurements, commands and events in real time and makes sure that everything works as it should. However, it is based on outdated technology that lacks modern security features, making it prone to unauthorized access and attacks.
On the other hand, ICCP has greatly simplified the sharing of data between different systems since the 1990s, playing an important role in managing the electric grid, scheduling, and billing. Even though it has good security features, it faces similar security problems to IEC 104 when connected with IT systems. For example, attackers have deployed a malware called “Industroyer” via the IT network, which misused the IEC 104 protocol to send instructions to control power substations and cause damage.
Measures to Improve Your Cyber Resilience
Creating separate networks, having strict controls on who can access what, and having a plan ready for responding to security incidents are key steps to improving security. For instance, ICCP uses so-called “Billateral Tables” to manage access control, for which security measures are often inadequate. If an attacker can gain access and modify them, they have access to the data of all control centers. Training OT and IT staff on these measures can significantly lower the risk of cyber threats. To keep these protocols secure, regular checks are required. These checks should focus on secure settings, prompt security updates, and constant monitoring to detect any unusual activity.
Convergence of IT and OT: A Secure and Technologically Advanced Future
The convergence of IT and OT represents a significant stride toward a secure digital future. Integrating security aspects into both domains ensures the resilience of industrial processes and digital ecosystems against cyber threats. By appreciating the distinct yet complementary roles of IT and OT, businesses can fortify their operations, guarantee data integrity, and pave the way for a secure and technologically advanced future.
Most of the above measures, such as network segmentation and a security incident response plan, are critical if the network is already compromised. If you want to know how cybercriminals gain access to networks in the first place and what you can do about it, you can read this article: Cyber Security: Guarding Against Unauthorized Access
If you already have measures in place, penetration testing or red teaming is a good way to assess the robustness of your security posture. If you need assistance on how to approach these or have any other questions related to cybersecurity, you can contact us.





