
Cybersecurity: Guarding Against Unauthorized Access
Learn about the most common initial attack vectors and their protection recommendations.
Browse through exciting articles, current news and helpful tips & tricks from our experts on all aspects of cybersecurity.

Learn about the most common initial attack vectors and their protection recommendations.

Emails are a Popular Entry Point for Attackers

A bug bounty program and a penetration test are both important measures to improve the security level of a system. However, there are important differentiators between the two that need to be understood before deciding which one to use.

Configuration of a local Windows firewall and what and how it can protect against.

Do you like listening to podcasts? Get to know the best five cyber security podcasts.

PDF (Portable Document Format) files are used on a daily basis both in the working world and by private individuals. This also makes them a popular tool for cybercriminals to use in phishing attacks. They allow direct execution of scripts that can reload additional malware.

Penetration test and red teaming are cybersecurity terms. But what exactly is red teaming? And what is a penetration test all about? What are the differences between the two terms?
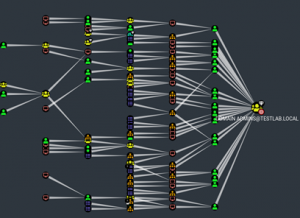
A modern Active Directory environment consists of many different components. There are clients, servers, databases, users, applications and much more. It is easy to lose track of everything (especially as a Red Team). The BloodHound tool can help here.

Computers often have strange behavior that cannot always be explained right away. Just because a laptop worked flawlessly the night before does not mean that problems won’t pop up out of nowhere the next day. In most cases, these are minor problems that can be solved quickly. However, it can also happen that the computer suddenly does not boot up at all and hangs during startup.

What are the most common security vulnerabilities in web applications? What does an attacker need to do to find and exploit them? And how can developers protect their web applications against them? Answers to these questions as well as practical hands-on examples are provided by PortSwigger’s Web Security Academy.
Never miss the latest news about cybersecurity topics again? Subscribe to our Newsletter.
Subscribe to our news feed on LinkedIn and register to receive our newsletter.
Don’t miss anything! Subscribe to our free newsletter.
Availability Monday to Friday 8:00 a.m. – 6:00 p.m (exception: customers with SLA – please call the 24/7 IRR emergency number).
Private individuals please contact your trusted IT service provider or the local police station.
For more information about our DFIR services here:
