Quick and Easy Guide to Finding the Right Password Manager
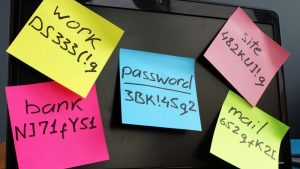
In an increasingly digital world where the security of corporate data is a top priority, every organization faces the challenge of protecting sensitive information from cyber threats. We are all familiar with the dilemma of having to remember long and complex passwords.









